AI-Infra-Guard
by TencentAI-Infra-Guard is a lightweight, efficient, and easy-to-use AI infrastructure security assessment tool that detects potential security risks in AI systems.
What is AI-Infra-Guard?
AI-Infra-Guard is an open-source, lightweight, and efficient AI infrastructure security assessment tool developed by Tencent. It is designed to detect and identify potential security risks in AI systems. The tool supports 28 AI framework fingerprints and covers over 200 security vulnerability databases. It is easy to use, requires no complex configuration, and offers flexible YAML rule definitions and matching syntax. AI-Infra-Guard is cross-platform compatible, resource-efficient, and supports various scanning methods, including local scanning, target scanning, and file-based scanning. It also integrates with external AI models for enhanced detection capabilities.
Key Features of AI-Infra-Guard
- Efficient Scanning: Supports fingerprint recognition for 28 mainstream AI frameworks and covers over 200 security vulnerability databases to detect known security risks.
- Vulnerability Detection: Provides detailed vulnerability information, including descriptions, severity ratings, and repair suggestions. Supports security assessments for various AI components like Gradio, JupyterLab, and Triton.
- Flexible Usage:
- Offers both WebUI and command-line interfaces to meet different user needs.
- Supports local scanning, single target scanning, multiple target scanning, and file-based scanning.
- Integrates with external AI models (e.g., Hunyuan) for deeper security assessments.
- Lightweight Design: The core components are efficient, with a small binary file size and low resource usage. It is cross-platform compatible, supporting Windows, Linux, and macOS.
- Easy to Extend: Users can customize rules as needed. The tool offers flexible matching syntax, supporting fuzzy matching, regular expression matching, and more.
Technical Principles of AI-Infra-Guard
- Fingerprint Recognition Technology: Sends HTTP requests to the target system, analyzes the response content (e.g., headers, body), and extracts feature information. It uses predefined fingerprint rules (stored in YAML files) and matching logic (e.g., regular expressions, fuzzy matching) to identify AI frameworks and components in the target system.
- Vulnerability Matching Mechanism: Matches identified AI components with entries in the vulnerability database. Vulnerability rules are defined in YAML format and include detailed information (e.g., descriptions, impact scope, repair suggestions). Logical operators (e.g., &&, ||) are used to combine multiple matching conditions, ensuring accurate vulnerability detection.
- AI Analysis Enhancement: Integrates with external AI models (e.g., Hunyuan) via API calls to obtain deeper analysis results. AI models are used to identify complex vulnerability patterns or provide intelligent detection suggestions.
- Lightweight Architecture: Core components are written in efficient programming languages (e.g., Go) to ensure performance and resource utilization. The modular design separates fingerprint recognition, vulnerability matching, and user interfaces, improving maintainability and scalability.
- Cross-Platform Support: Compiled as static binary files, the tool can run on different operating systems, including Windows, Linux, and macOS.
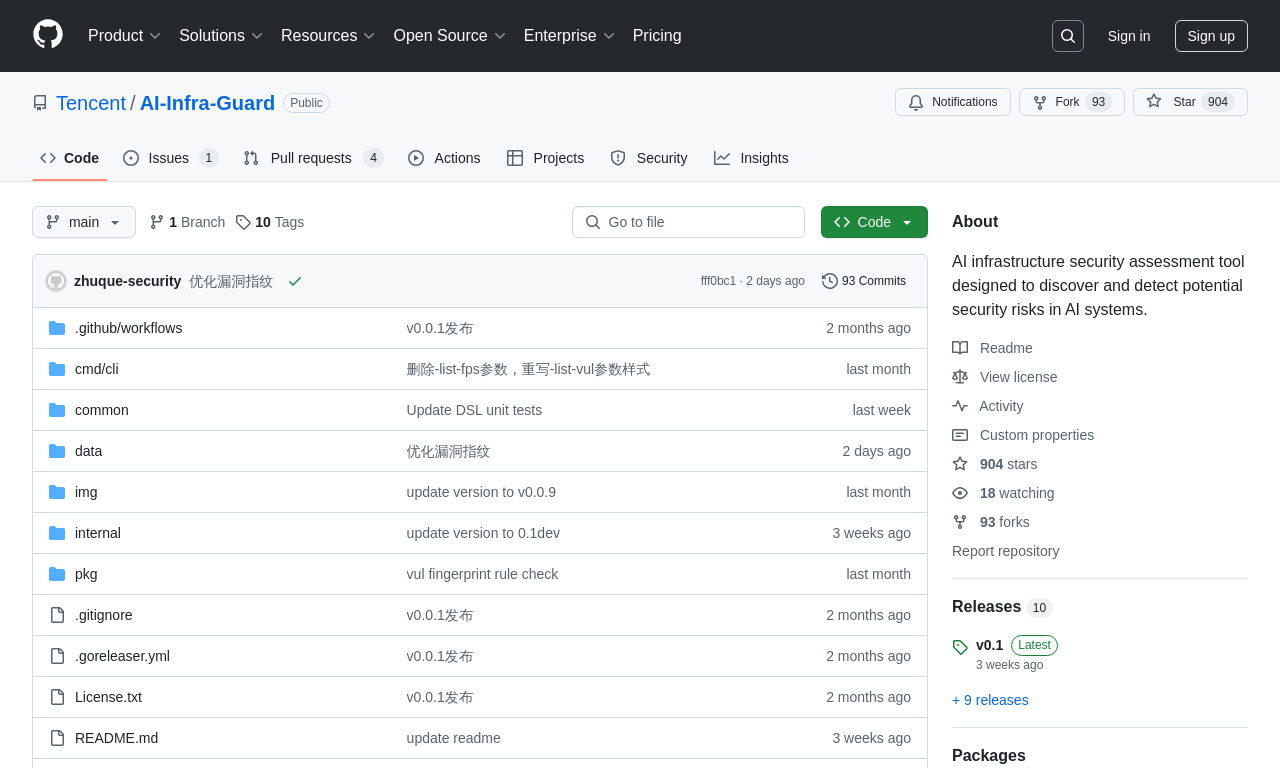
Project Address of AI-Infra-Guard
- GitHub Repository: https://github.com/Tencent/AI-Infra-Guard
Application Scenarios of AI-Infra-Guard
- AI Development and Deployment: Helps development teams quickly detect security vulnerabilities in frameworks and components during AI model development and deployment, ensuring system security.
- Cloud Service Security: Scans AI services on cloud platforms to identify and repair vulnerabilities, ensuring user data and platform security.
- Security Audits and Compliance: Supports enterprises in conducting security audits, generating vulnerability reports, and meeting industry compliance requirements.
- IT Operations Management: Enables enterprise IT teams to regularly scan AI systems, monitor security status, and quickly respond to and repair issues.
- Security Research and Community Contributions: Researchers and the community can study new vulnerability detection methods and contribute new fingerprints and vulnerability rules.
Features & Capabilities
What You Can Do
Security Risk Detection
Vulnerability Assessment
Ai Framework Fingerprinting
Cross-Platform Scanning
Categories
AI Security
Vulnerability Detection
Open Source
Cross-Platform
Lightweight
Efficient
YAML Rules
External AI Integration
Security Assessment
AI Frameworks
Example Uses
- AI Development and Deployment
- Cloud Service Security
- Security Audits and Compliance
- IT Operations Management
- Security Research
Getting Started
Pricing
free
Screenshots & Images
Primary Screenshot
Additional Images
Stats
91
Views
0
Favorites
